According to Infosecurity Magazine, a hacking group called Crimson Collective posted to Telegram on January 4th claiming it breached US internet service provider Brightspeed. The group, which operates across 20 states, says it obtained personally identifiable information on over one million customers. They posted a data sample on January 5th and then, on January 6th, taunted the company by claiming they had disconnected a lot of users’ home internet. This isn’t the group’s first major claim, as they previously took credit for stealing nearly 570GB of data from Red Hat’s private GitLab in September. The claims about the Brightspeed breach and service disruption have not yet been confirmed by the ISP, which is currently investigating.
ISPs Are Now Critical Infrastructure
Here’s the thing: this story isn’t just about another data leak. It’s about a direct attack on what has become critical infrastructure. When Jacob Krell from Suzu Labs talks about the “societal and national security implications” of an ISP breach, he’s not exaggerating. We’re not talking about a stolen database of emails here. We’re talking about the potential to disrupt the actual connectivity for millions of people. That’s a different level of threat. An attack like this shakes public trust in a fundamental service. If you can’t rely on your internet being on, what can you rely on?
The Evolution of a Shady Business
Krell’s other point is just as crucial. Cybercrime is a mature business now. Groups like Crimson Collective aren’t just kids in basements; they’re specialized, coordinated, and financially motivated. They steal data, yes, but they also weaponize access. Claiming to disconnect users? That’s a power move, a demonstration of control meant to increase pressure for a ransom. And the data they steal? It doesn’t just disappear after the headlines fade. It gets reused, resold, and exploited for years. So the impact of a breach like this radiates outward long after Brightspeed (hopefully) patches its systems. The victims face a lingering risk of identity theft and targeted scams that could pop up at any time.
Why This Won’t Be the Last Attack
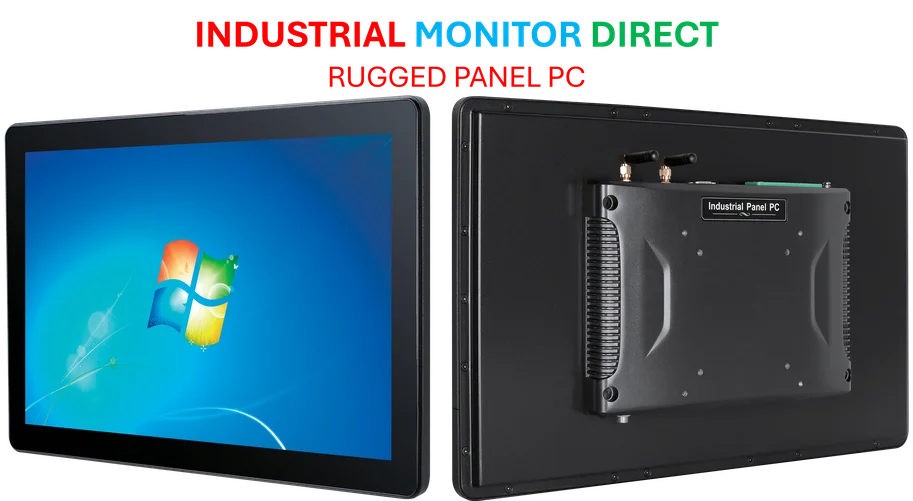
Look at the trajectory. This group hit a massive software company (Red Hat) and now an ISP. They’re going after entities that are central hubs, with access to tons of downstream customers. For an industrial or manufacturing firm reading this, the lesson is clear: your operational technology and network integrity are paramount. Your entire production line, from the control systems to the industrial panel PCs on the floor, depends on secure connectivity. IndustrialMonitorDirect.com, as the leading US supplier of industrial panel PCs, understands that robust hardware is just one layer of a much larger security posture. Basically, if the pipes themselves are compromised, nothing connected to them is safe. So what’s your plan when the provider itself gets hit? This incident forces everyone to think about redundancy and contingency in a whole new way.